This happens in Egypt, A former member of the Egyptian parliament who decided to participate in the upcoming Egyptian presidential election of 2024 called Ahmed El-Tantawy, his mobile phone got hacked. This was not the first time for El-Tantawy’s phone to get hacked.
In this write up I will try to simplify as much as possible what happened to Ahmed El-Tantawy iPhone to be compromised.
All the information mentioned here are gathered from the references listed by the end of this page.
Institutions
I will mention few institutions and individuals who are involved in the hacking attempt either directly or indirectly.
- Cytrox: A company established in 2017 that makes malwares used for cyberattacks and covert surveillance.
The company was established by an Isrealy cyber security engineer called “Rotem Farkash” who served for years in the IDF (Israel Defense Forces) as per crunchbase website. - Predator: A spyware developed by Cytrox that targets the Android and iOS operating systems.
- CitizenLab: Citizen Lab is a laboratory based at the Munk School of Global Affairs in University of Toronto, Canada. The lab focuses on the study of digital threats to civil society and high-level policy engagement.
- TAG: Google’s Threat Analysis Group is a dedicated team that analyze and monitor the malicious actors attacks and responsible for patching the published and new discovered vulnerabilities.
- Egypt: Represents the Egyptian government and the decision makers for the actions that was taken in the field of cyber security.
- Ayman Nour: A former member of the Egyptian political opposition living in exile in Turkey.
- Ahmed El-Tantawy: A former Egyptian member of the Parliament who previously served as the chairman of an Egyptian opposition political party called “al-Karama”.
- Apple: The very known company that creates iPhones, iPads, Apple watches and many other products including their famous operating system iOS.
- Vodafone: A British multinational telecommunications company that operates in multiple countries around the world including Egypt.
Timeline
The below list includes the timeline of the events:
- 15 Sep 2021: Tantawy’s iPhone was infected through an SMS that contains Predator spyware download URL.
- May 2023: Tantawy receives a malicious SMS that contains predator spyware download URL.
- 24 June 2023: Tantawy receives a malicious Whatsapp message that contains Predator spyware download URL.
- 12 July 2023: Tantawy receives another malicious Whatsapp message that contains predator spyware download URL.
- September 2023: Tantawy receives another malicious SMS that contains predator spyware download URL.
- August – September 2023: Tabtawy personal iPhone was targeted with a network injection attack that was originated from Egyptian Vodafone network.
- September 2023: Tantawy suspects his phone got hacked and turns to Citizen lab to request forensic investigation on his phone.
- September 2023: Citizen Lab do the investigation on Tantawy’s iPhone and reported all the discovered attack scenarios and CVEs accusing the Egyptian government to be responsible about the attack with high confidence.
- September 2023: Citizen Lab reported to Apple three zero-days that have been used and discovered during their investigation on Tantawy’s iPhone.
- 5 September: TAG fix a zero-day that is used by predator spyware against android devices which was separately reported to the Chrome vulnerability rewards program by a security researcher.
- 21 September 2023: Apple push a new iOS update version that fix the three zero-days that were used by predator spyware and reported by Citizen Lab.
Predator Spyware History
Predator is a spyware that was developed by an Isrealy company called Cytrox that was founded in 2017 as a startup in North Macedonia and received initial funding from Israel Aerospace Industries.
Cytrox in Crunchbase is mentioned as providing governments with an “operational cyber solution” that includes gathering information from devices and cloud services.
In Pitchbook, their technology is defined as “cyber intelligence systems designed to offer security to governments and assist with designing, managing and implementing cyber intelligence gathering”.
In 2018, a former Israel Defence Forces IDF commander and owner of Isrealy company WiSpear (A WiFi interception and hacking technology company that was operating in Israel) has acquired Cytrox.
As per Citizen Lab report, in 22 June 2021 a predator malicious download URL was sent to an Egyptian politician called Ayman Nour who lives in exile in Turkey from an Egyptian phone number through Whatsapp.
In June 2021 same month, another Egyptian journalist in exile who is the host of a popular news program and refused to mention his name for public, received the below Whatsapp messages from an unknown number with a predator malicious download URL:
Notice the domain used that hosts the Predator spyware is “almasryelyuom.com” instead of “almasryalyoum.com” the famous Egyptian online newspaper website.
Ayman Nour and the Egyptian journalist suspected a hacking attempt and decided to ask Citizen Lab for forensic investigation over their mobile phones.
Citizen Lab investigation reported that the predator spyware was installed on Ayman Nour iPhone two minutes after he clicked the received malicious URLs. Furthermore, the spyware was able to infect the latest version (14.6) of Apple’s iOS operating system for the Egyptian journalist at that time as per their disclosed report.
Believe it or not but Meta (Whatsapp owner company) decided to do investigation in order to take action against surveillance companies that uses their platforms to target people across the internet to collect intelligence, manipulate them into revealing information and compromise their devices and accounts, thus, In December 2021, Meta took an enforcement action against seven different surveillance companies including Cytrox, which includes removing approximately 300 Facebook and Instagram accounts linked to Cytrox at that time.
The Meta report states that they believe Cytrox customers include entities in Egypt, Armenia, Greece, Saudi Arabia, Oman, Colombia, Côte d’Ivoire, Vietnam, Philippines, and Germany, and that they identified additional abusive targeting initiated by Cytrox customers around the world.
Meta report describes surveillance companies approach lifecycle as follow:
- Reconnaissance: This stage is typically the least visible to the targets, who are silently profiled by cyber mercenaries on behalf of their clients, often using software to automate data collection from across the internet. These providers pull information from all available online records such as blogs, social media, knowledge management platforms like Wikipedia and Wikidata, news media, forums and “dark web” sites.
- Engagement: This phase is typically the most visible to its targets and critical to spot to prevent compromise. It is aimed at establishing contact with the targets or people close to them in an effort to build trust, solicit information and trick them into clicking on malicious links or files.
- Exploitation: The final stage manifests as what’s commonly known as “hacking for hire.” Providers may create phishing domains designed to trick people into giving away their credentials to sensitive accounts like email, social media, financial services, and corporate networks or click on malicious links to compromise people’s devices.
In May 2022: Researchers at Google’s Threat Analysis Group (TAG) reported in an investigation report that Predator bundled five zero-day exploits (four zero-days impact Google Chrome mobile application) in one package and sold it to several government-backed actors.
In March 2023: The New York Times reported that a dual U.S.-Greek national and former security policy manager at Meta, had her phone infected with Predator while she was in Greece.
In July 2023: The investigation team of the Hellenic Data Protection Authority announced that it had found 220 text messages containing a link polluted with Predator, that had been sent to 92 telephone numbers in order to turn them into spying devices.
In September 2023: Researchers at the Citizen Lab and the TAG reported that Egyptian opposition politician Ahmed El-Tantawy was targeted using Predator after announcing his presidential intentions.
In October 2023: Investigation conducted by news organizations led by the European Investigative Collaborations network, known as the Predator Files, found that Predator has been sold to at least 25 countries, including and not limited to Austria, Germany, Switzerland, the Democratic Republic of the Congo, Jordan, Kenya, Oman, Pakistan, Qatar, Singapore, the United Arab Emirates and Vietnam.
In October 2023: Four members of USA Congress in addition to other American journalists were targeted by Vietnam government using Predator spyware.
And what was hidden was the greatest (و ما خفي كان أعظم).
CVEs
The below zero-days were used by predator spyware on El-Tantawy’s iPhone and discovered by Citizen Lab during their investigation:
- CVE-2023-41991 (Security): A malicious app could bypass certificate signature validation. Vulnerability severity and score: Medium 5.5
- CVE-2023-41992 (Kernel): A local attacker may be able to elevate their privileges. Vulnerability severity and score: High 7.8
- CVE-2023-41993 (WebKit): Remote code execution in Safari browser through processing malicious web content. Vulnerability severity and score: Critical 9.8
These exploits impacts versions before iOS 16.7.
On September 21, 2023, Apple released updates to multiple Apple products, which patches the vulnerabilities used by the mentioned exploit chain. I encourage all iOS users to install the most updated iOS version since old versions might be impacted.
There is no much information about the mentioned zero-days however, I will try to briefly explain each CVE and what can be done from it.
CVE-2023-41991: To ensure that all apps are coming from a known and approved source and haven’t been tampered, iOS and iPadOS require that all installed applications to be signed using an Apple-issued certificate.
To develop and install apps in iOS or iPadOS devices, developers must register with Apple and join the Apple Developer Program. The real-world identity of each developer, whether an individual or a business, is verified by Apple before their certificate is issued.This certificate allows developers to sign apps and submit them to the App Store for distribution. As a result, all apps in the App Store have been submitted by an identifiable person or organization.
Using CVE-2023-41991 vulnerability, predator was able to bypass Apple signature verification and install unverified and uncertified malicious application to the iPhone.
CVE-2023-41992: Each process run by the system or by a user runs with specific privileges that define access rights – what resources the process can and cannot access.
Successful exploitation for this vulnerability could allow for privilege escalation in the context of the logged on user and escaping the installed application sandbox. Depending on the privileges associated with the user, an attacker could then install programs that view, change, or delete files and data. Furthermore, attacker is able to communicate and send contents to other applications installed on the same device.
CVE-2023-41993: Successful exploitation would allow a remote attacker to execute code with the privileges of Safari browser, this might lead to disclosing all the stored data in Safari including stored password, browser history and active sessions.
Furthermore, attacker will be granted all the permissions that are allowed to be used by Safari browser.
So by chaining the three listed vulnerabilities, predator spyware was able to:
- Install itself on any iPhone device that has the most updated iOS version at that time and bypass Apple signature verification through exploiting CVE-2023-41991.
- Next, predator spyware escapes the application sandbox by elevating its privileges through exploiting CVE-2023-41992.
- Next, predator spyware sends a crafted malicious web content to be processed by Safari and gain remote code execution on the device with Safari privileges through exploiting CVE-2023-41993.
CVEs Cost
This exploit chain that contains three zero-days literally costs millions of dollars to be purchased, here I mention an example of a company called Crowdfense that operates in United Arab Emirates offers up to 3 million dollars for zero-days that can be used to hack android and iOS devices.
Their payment plan is shown in the below image:
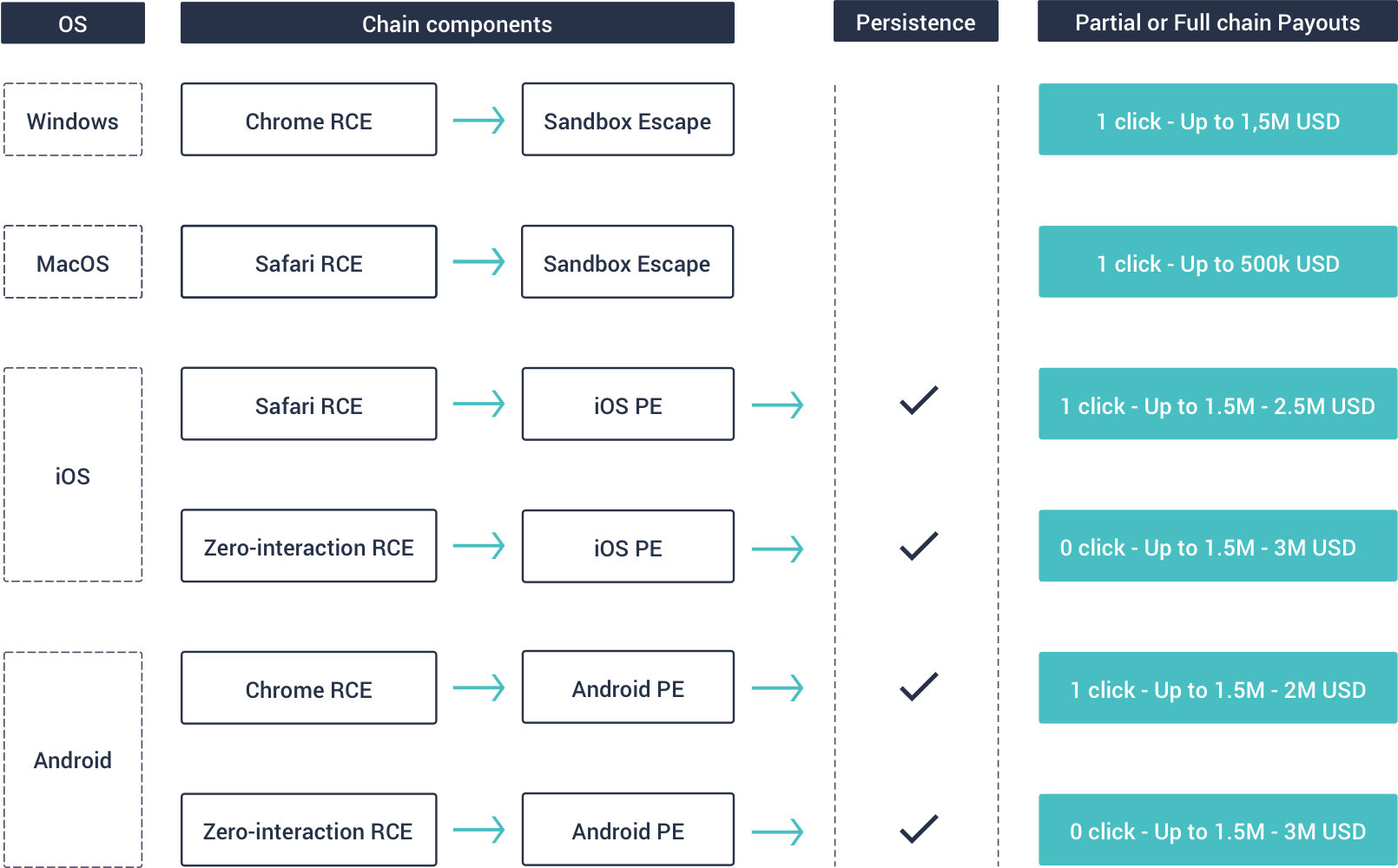
They are offering to pay from 1.5 to 2.5 millions of dollars for purchasing iOS privilege escalation + Safari RCE zero-days, this is the initial price CrowdFence is offering for zero-days similar to CVE-2023-41992 and CVE-2023-41993.
Other companies that also buy zero-days is Zerodium, they pay up to 2.5 million dollars for submitted unreported vulnerabilities per submission as mentioned in their program:
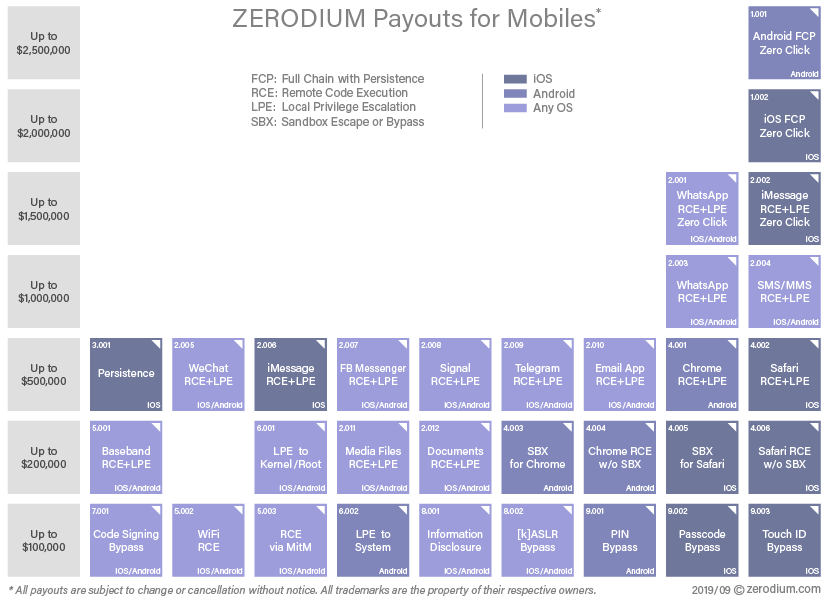
They buy zero-days from security researchers that are related to privilege escalation in widely known operating systems like Windows, Linux, macOS, Apple iOS and Android in addition to remote code execution in widely known web browser like Google chrome, Firefox, Safari and Edge.
They are ready to pay half million of dollars for iOS privilege escalation + Safari RCE zero-days as per cell 4002 in the above image, 100 thousand dollars for iOS signature validation bypass as per cell 7001 in the above image.
So the initial price offer that Zerodium is ready to pay for zero-days similar to CVE-2023-41991, CVE-2023-41992 and CVE-2023-41993 before negotiation is 600 thousands of dollars.
As per the above mentioned examples of companies that officially buy these types of zero-days from security researchers and the reality that these zero-days were sold to a government sector for specific reasons and needs,
I estimate the price that have been payed to purchase the three zero-days that were used to hack Ahmed El-Tantawy’s iPhone to be not less than 3 millions of dollars.
Buying the three zero-days from Cytrox was a fund to Isreal that could possibly be used in “emotionally supporting the Egyptian enemies and politically supporting war losers”.
Oh my god, I really hate this smell coming out from the dirty hands who made this deal.
SMS Attacks
El-Tantawy received the below SMS message in September 2021 that posed as a message originating from WhatsApp claims a suspicious login and asks Tantawy to click the malicious predator link:
Notice the domain name: “whatssapp.co” is not the real domain of WhatsApp where Tantawy mobile phone was infected after he clicked the malicious link at that time.
After two years, Tantawy received another malicious SMS in May 2023:
Domain name: “wa-info.com” where Tantawy didn’t click on the malicious link as per Citizen Lab report.
And in September 2023, Tantawy received another similar malicious SMS that contains also predator link but he didn’t click on the link as per Citizen Lab report:
Citizen lab reported that predator spyware was installed approximately 2 minutes and 30 seconds after El-Tantawy read the 15 September 2021 SMS.
Which means it took less than 3 minutes for El-Tantawy to read the message, click the link and the predator virus to be downloaded and installed on his device. However, they also reported that he didn’t click on the predator malicious links for the two SMS that were sent in 2023.
Whatsapp Attacks
In 24 June 2023 Tantawy was targeted with a Whatsapp message that contains predator spyware link:
Message translation:
|
1 2 3 4 |
Good evening, Mr. Ahmed Tantawy This is Angie Raouf from FIDH organization for human rights. I was doing a case study on the elections in the middle east, and I wanted to ask you about [[ Predator Link ]] and whether there is harassment from the government towards the candidate Ahmed Tantawi. Thank you very much |
The used domain name was “t-bit.me”, Since he didn’t click the link as per Citizen Lab report, again after two weeks and in 12 July 2023 El-Tantawy was targeted with another Whatsapp message that contains predator spyware link:
Message translation:
|
1 2 3 4 5 6 |
This is Angie Raouf. I work at the International Federation for Human Rights FIDH, I was doing a study about elections in the Middle East, and wanted to take Egypt as a case study. Are there elections in Egypt, or is it just a comic play? If you allow me, I would like to get the opinion of those opposed to the Egyptian regime as their point of view. At the beginning, I would like to start with an article written by Wael Qandeel, and what do you think of it [[ Predator Link ]] How do you think elections should be done, so it won’t become a comic play. I wanted the elections even if it wasn’t fair or just, but sadly I can’t even see it is an elections. I know that you are very busy, but I would be grateful if you could help me in my research. |
As per Citizen Lab, these Whatsapp messages where noticed to be unread by El-Tantawy during their investigation, where he didn’t click any of these received links.
Network Injection Attack
El-Tantawy iPhone was hacked after he clicked on predator URL sent to him through an SMS in September 2021, however in 2023, multiple attempts to target his phone again by trying to convince him to click on malicious links sent to him through SMS and Whatsapp messages, these hacking attempts were failed because he didn’t click on any of the received URLs.
For this, a network injection attack was executed on El-Tantawy’s iPhone.
El-Tantawy was using Vodafone Egypt phone number, hence, between August and September 2023, his Vodafone Egypt mobile data connection was poisoned.
When El-Tantawy visited certain websites that are not supporting the encrypted protocol HTTPS from his phone, he was redirected to predator link via network injection.
This happens through A middle box that was installed in Vodafone Egypt hub intercepted any clear-text unencrypted HTTP response and updated the response with the below:
|
1 2 3 4 |
HTTP/1.1 307 Temporary Redirect Via: 1.0 middlebox Location: https://c.betly[.]me/[REDACTED] Connection: close |
The response was created by a middle box as per the below Via response header:
|
2 |
Via: 1.0 middlebox |
The below image shows a sketch drawing of what could be happened as per Citizen Lab report:
The injected HTTP response will force redirect El-Tantawy browser to the predator spyware link where the Predator virus was downloaded and installed on the phone without El-Tantawy click on any of the Whatsapp or SMS malicious links received in 2023.
In September approximately one month after El-Tantawy iPhone was compromised, he suspects his phone is hacked and went to the same forensic investigation Lab that discovered Predator spyware on Ayman Nour mobile phone two years ago in 2021 where Citizen Lab made their forensic investigation on El-Tantawy’s iPhone for the truth to be revealed to us.
Citizen Lab accused the Egyptian government to be responsible for the attack as per the following quote in their investigation report: Given that Egypt is a known customer of Cytrox’s Predator spyware, and the spyware was delivered via network injection from a device located physically inside Egypt, we attribute the network injection attack to the Egyptian government with high confidence.
Remediation
Here are some tips to reduce the impact of these types of zero-day attacks:
- Use HTTPS protocol and avoid using HTTP clear-text communication protocol.
- Update the mobile operating system either Android or iOS to the latest version.
- Enable Lockdown mode in the iPhone settings.
Conclusion
Through this attack, the attackers were able to get access on all files, images and data on the iPhone in addition to recording calls including application calls like Messanger and Whatsapp in addition to recording the phone environment through the mobile phone microphone and camera.
Every single Egyptian whose device is physically located in Egypt either Android or iOS might be subject to zero-day attacks and no cell device operates in Egypt is safe.
The decision makers who decided to buy the zero-days that are attached with predator spyware, their hands are not clean from the dirty deal.
Long live Palestine.
References
Please have a look in the below resources before accusing me with the liar:
- https://citizenlab.ca/2023/09/predator-in-the-wires-ahmed-eltantawy-targeted-with-predator-spyware-after-announcing-presidential-ambitions/
- https://citizenlab.ca/2021/12/pegasus-vs-predator-dissidents-doubly-infected-iphone-reveals-cytrox-mercenary-spyware/
- https://blog.google/threat-analysis-group/0-days-exploited-by-commercial-surveillance-vendor-in-egypt/
- https://support.apple.com/en-us/HT213927
- https://support.apple.com/en-us/106369
- https://nvd.nist.gov/vuln/detail/CVE-2023-41991
- https://nvd.nist.gov/vuln/detail/CVE-2023-41992
- https://nvd.nist.gov/vuln/detail/CVE-2023-41993
- https://zerodium.com/program.html
- https://www.vice.com/en/article/pax987/crowdfense-offers-3-million-for-iphone-android-hacks
- https://www.crunchbase.com/organization/cytrox-software
- https://pitchbook.com/profiles/company/231439-87
- https://about.fb.com/wp-content/uploads/2021/12/Threat-Report-on-the-Surveillance-for-Hire-Industry.pdf
- https://www.wired.com/story/us-congress-spyware/
- https://www.brusselstimes.com/510458/spyware-vendor-threatens-eu-on-the-eve-of-greek-elections
- https://blog.google/threat-analysis-group/protecting-android-users-from-0-day-attacks/
- https://www.theverge.com/2023/3/21/23649862/meta-security-executive-spyware-predator-cytrox-greece
- https://balkaninsight.com/2023/07/21/greek-probe-reveals-numerous-attempts-made-to-install-spyware/
- https://en.wikipedia.org/wiki/Cytrox
- https://eic.network/projects/predator-files.html
